Last week, the popular Easy WP SMTP plugin for WordPress, installed on more than 500,000 sites, was patched with a serious administrator password reset vulnerability. This plugin allows site owners to configure SMTP settings for outgoing email from their site.
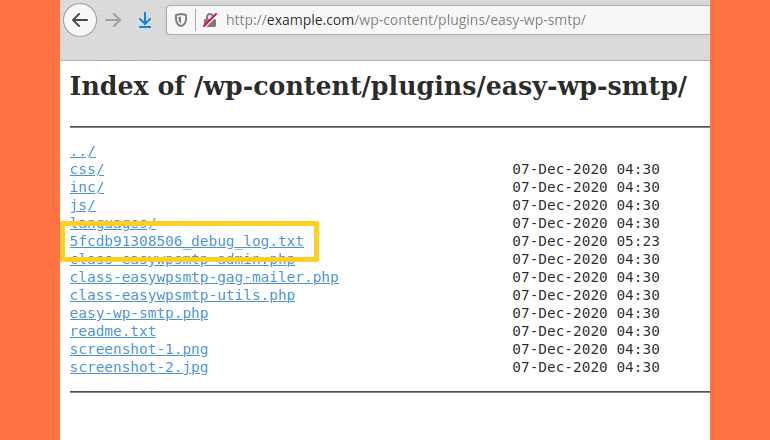
According to researchers from Ninja Technologies Network, Easy WP SMTP version 1.4.2 and later contains a feature that generates debug logs for all emails sent by a site, which are then saved in the installation folder. “There is no index.html file in the plug-in folder, and therefore, on servers where the directory listing is included, hackers can find and view this log,” the experts explain.
WordPress Zero Day Vulnerability Details :
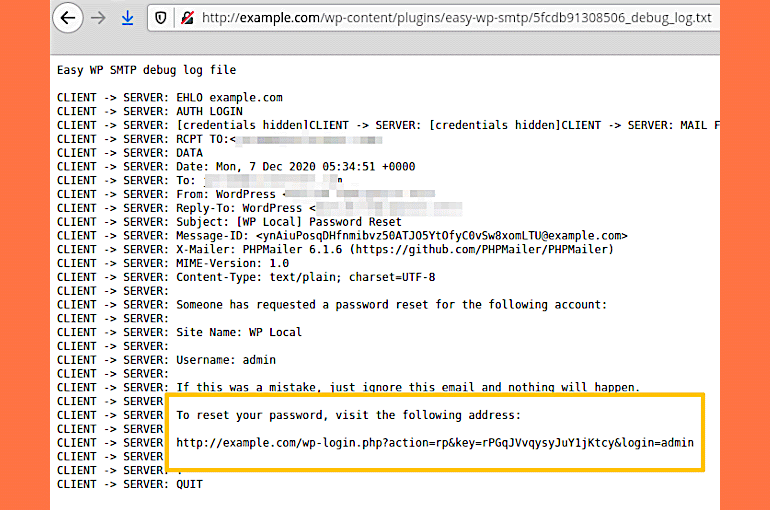
Experts warn that automated attacks have been directed at sites with vulnerable versions of the plugin for about two weeks, the purpose of which is to identify the administrator account and then initiate a password reset for it. The fact is that to reset the administrator password, you need to send an email with a special link, and this letter also ends up in the Easy WP SMTP logs. Basically, all an attacker needs to do is access the debug log, find the password reset link there, and hijack the site administrator account.
As mentioned above, the plugin developers have already fixed the vulnerability. The patch is included in Easy WP SMTP version 1.4.4 .
It should be noted that this is not the first critical bug in Easy WP SMTP. So, in 2019, a problem was discovered in the plugin that allowed third parties to enable user registration and then create new administrator accounts.