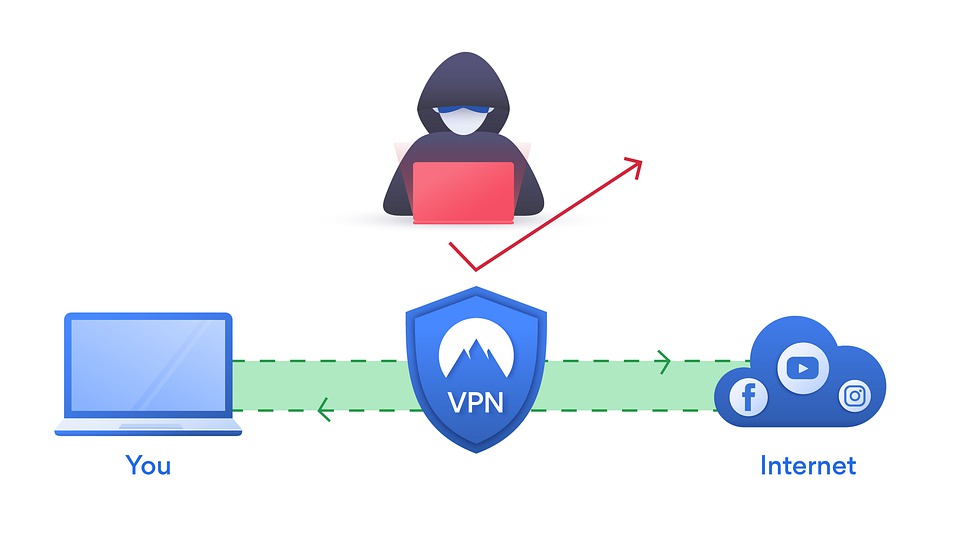
VPN have been one of the “stars” of this pandemic era. Office workers and companies alike relied upon it so much that it has become ubiquitous.
But not all its applications appear to be trouble free. Cybersecurity researchers from Claroty have discovered a number of critical vulnerabilities in industrial VPN implementations, primarily used to provide remote access to operational technology (OT) networks that could allow hackers to overwrite data, execute malicious code, and compromise industrial control systems (ICS).
In their report they successfully demonstrates multiple severe vulnerabilities in enterprise-grade VPN installations, including Secomea GateManager M2M Server, Moxa EDR-G902, and EDR-G903, and HMS Networks eWon’s eCatcher VPN client.
There are more often than not found in sectors like oil and gas and water utilities, and are used to remotely access, maintain and monitor ICS and field devices, including programmable logic controllers (PLCs) and input/output devices.
The researchers believe that a successful exploitation of these flaws could allow an attacker to get into ICS devices and wreck havoc
GateManager under threat
One of the devices under intense scrutiny was Secomean’s GateManager.
There the researchers found a critical vulnerability, CVE-2020-14500, that grands the ability to the would be attacker of overwriting arbitrary data, executing arbitrary code, or causing a DoS condition, running commands as root, and obtaining user passwords due to the use of a weak hash type.
The product is one of the most widely used ICS remote access server deployed worldwide as a cloud-based SaaS solution that allows users to connect to the internal network from the internet through an encrypted tunnel while avoiding server setups.
In detail, the critical flaw found, occurs due to improper handling of some of the HTTP request headers provided by the client.
It can be exploited remotely and without requiring any authentication to achieve remote code execution, which could result in gaining full access to a customer’s internal network, along with the ability to decrypt all traffic that passes through the VPN.
Other products interested were Moxa EDR-G902 and EDR-G903 industrial VPN servers. A stack-based buffer overflow bug (CVE-2020-14511) that can be triggered just by sending a specially crafted HTTP request, was found by the researchers. This could eventually allow attackers to carry out remote code execution without the need for any credentials.
Claroty researchers also tested HMS Networks’ eCatcher, a proprietary VPN client that connects to the company’s eWon VPN device, and found that the product is vulnerable to a critical stack-based buffer overflow (CVE-2020-14498) that can be exploited to achieve remote code execution.
All an attacker needs to do is to carry out a Social engineering attack and make their victims click on a email o web link containing a specifically crafted HTML element that triggers the flaw in eCatcher, eventually allowing attackers to take complete control of the targeted machine.
All three vendors were notified of the vulnerabilities and responded quickly to release security fixes that patch their products’ loopholes.
Secomea users are recommended to update their products and HMS Networks users are advised to update eCatcher to its latest version as well.