The Transport Layer Security (TLS) might just be not so secure thanks to new vulnerability that could potentially allow an attacker to break the encryption and read sensitive communication under specific conditions.
Called Raccon Attack, this exploit uses a side-channel in the cryptographic protocol (versions 1.2 and lower) to extract the shared secret key used for secure communications between two parties.
As explained in this paper: “The root cause for this side channel is that the TLS standard encourages non-constant-time processing of the DH secret. If the server reuses ephemeral keys, this side channel may allow an attacker to recover the premaster secret by solving an instance of the Hidden Number Problem.”
In short, this is a brand new timing attack.
The would be Criminal Hacker willing to break the security wall created by the TLS Handshake will have to record the handshake messages between a client and server and subsequently measure the time it takes for the server to respond to the operations involved in deriving the shared key.
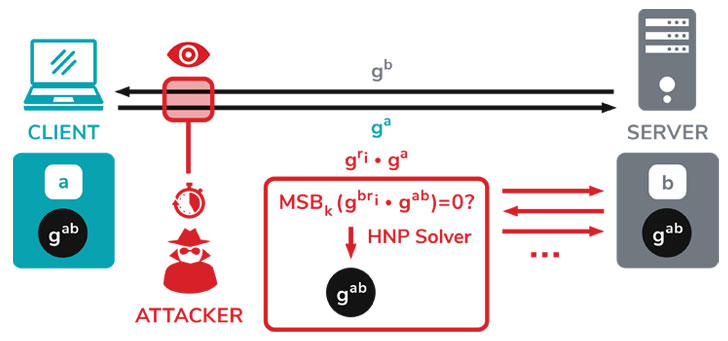
Assuming the attacker can identify this edge case, it allows the bad actor to decipher the secret key of the original handshake and ultimately decrypt the TLS traffic to recover its contents in plaintext.
Not so easy right now
Luckly Raccoon is a complex timing attack and it is very hard to exploit. It requires a lot of stars to align to decrypt a real-world TLS session. But in the case the (rare) circumstances are met, Raccoon allows an attacker to decrypt the connection between users and the server. This typically includes, but is not limited to, usernames and passwords, credit card numbers, emails, instant messages, and sensitive documents.
But then again the attacker needs particular circumstances for the Raccoon attack to work. He needs to be close to the target server to perform high precision timing measurements. He needs the victim connection to use DH(E) and the server to reuse ephemeral keys. And finally, the attacker needs to observe the original connection. For a real attacker, this is a lot to ask for. However, in comparison to what an attacker would need to do to break modern cryptographic primitives like AES, the attack does not look complex anymore. But still, a real-world attacker will probably use other attack vectors that are simpler and more reliable than this attack.
So in the end, for now Raccoon is just a cautionary tale, as the researchers put it: “In this context, Raccoon teaches a lesson for protocol security: For protocols where some cryptographic secrets can be continuously queried by one of the parties, the attack surface is made broader. The Raccoon attack showed that we should be careful when giving attackers access to such queries.”





