Researchers from BlackBerry conducted an analysis of the DarkCrystal RAT (aka DCRat) malware and the activity of its developer on the dark web. Apparently, the malware has been active since 2019, is the “brainchild” of a Russian-speaking developer, and sells for as little as 500 rubles (about $7) for two months or 4,200 rubles (about $60) for a lifetime license.
The company’s report notes that such a low price is a rather unusual phenomenon, which gives the impression that the author of the malware, known by the nicknames boldenis44, crystalcoder and simply Koder, is not looking for profit at all, has an alternative source of funding, or, probably, DarkCrystal is his personal project, not his main source of income.

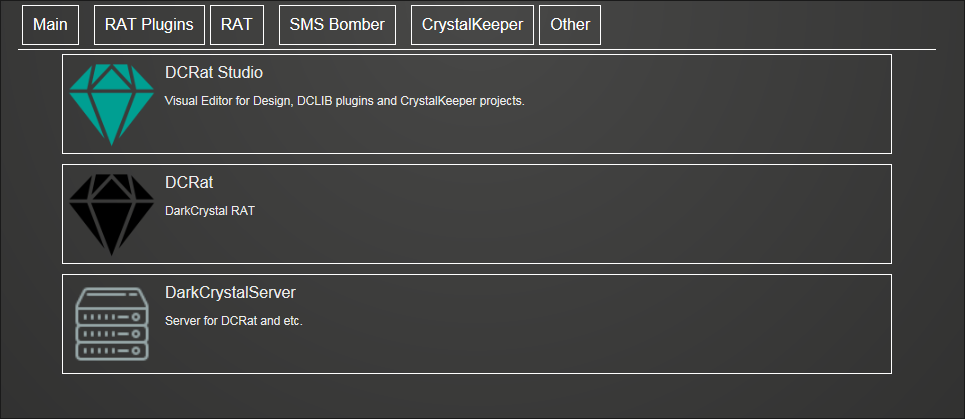
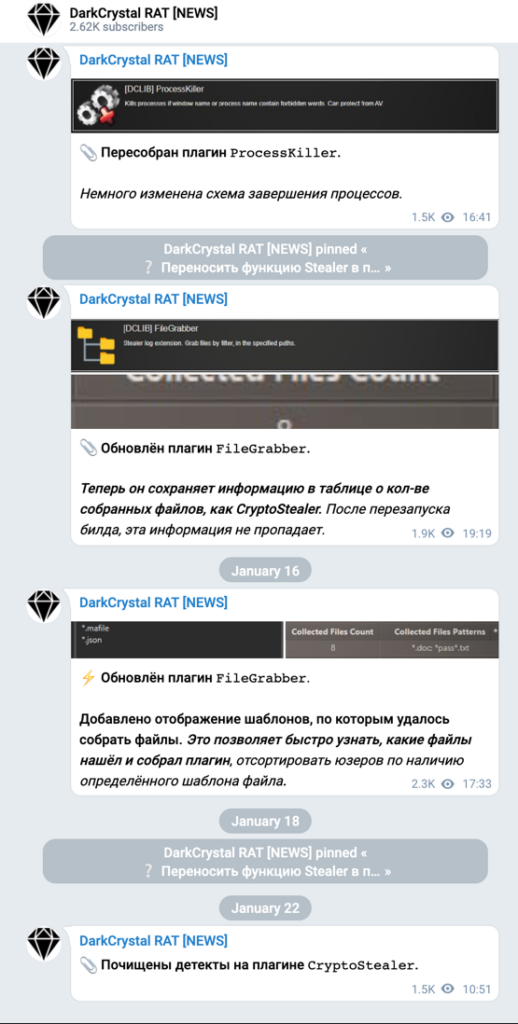
DarkCrystal is written in .NET and has a modular design, which can be used for a variety of tasks, including dynamic code execution, data theft, surveillance, and DDoS attacks. Interestingly, the functionality can be extended with third-party plugins developed by affiliates using a dedicated DCRat Studio IDE, and subscribers are given access to a list of supported plugins.
Once launched on the victim’s computer, the malware collects system information and transfers data such as host and user names, location data, privileges, installed security solutions, motherboard and BIOS information, and Windows versions to the command and control server.
DarkCrystal is capable of taking screenshots, intercepting keystrokes and stealing various types of data from the system, including the contents of the clipboard, cookies, passwords, browser history, bank card data, as well as Telegram, Discord, Steam, FileZilla accounts.
Three components are included in the “product” itself: the stealer/client executable, the C&C interface, and the JPHP executable, which is a tool for the administrator. The latter is designed in such a way that a hacker can silently activate the “breaker”, that is, an attacker can remotely make the tool unusable. It also allows subscribers to communicate with the C&C server, issue commands to infected endpoints, and send error reports to the malware author.
Currently, DarkCrystal RAT is hosted on crystalfiles[.]ru, where it “moved” from dcrat[.]ru, a simple site that was used only for downloading. Since a previous analysis of the malware by Mandiant experts in May 2020 traced the RAT infrastructure to files.dcrat[.]ru, the switch to crystalfiles[.]ru, according to BlackBerry experts, indicates that the malware author is responding to a public disclosure information.
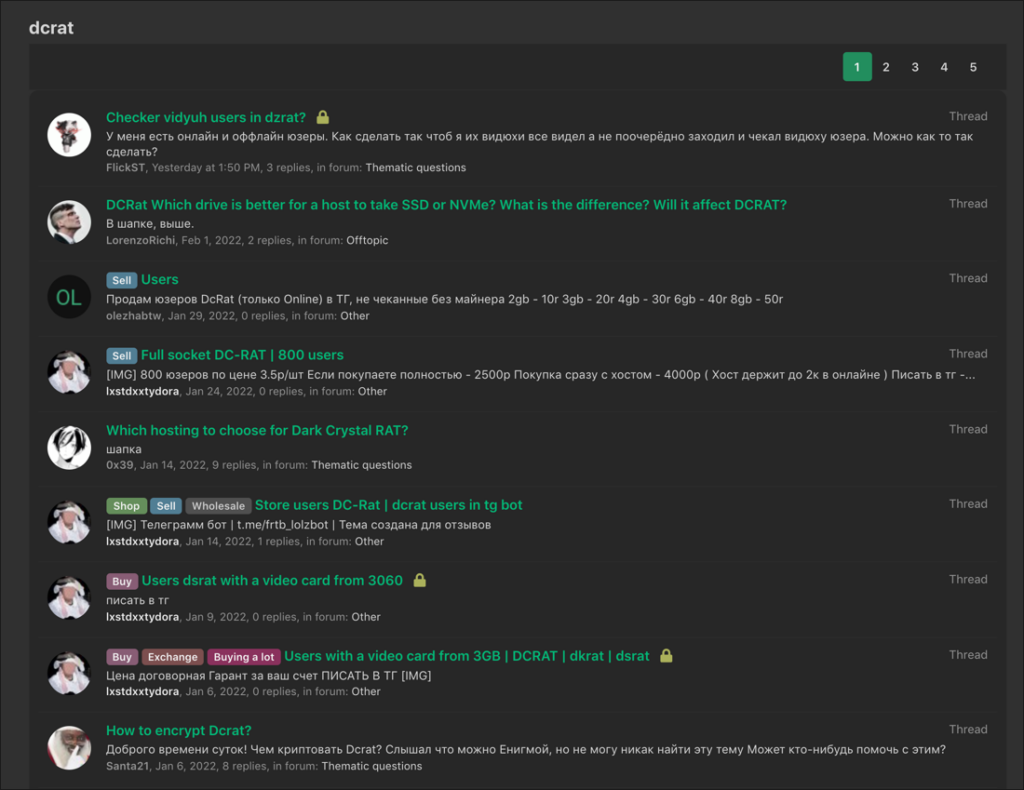
Operations for the sale and advertising of malware are now carried out through Russian-language hack forums (including lolz[.]guru), and news and updates are published in Telegram.
The count also states that Cobalt Strike and TDS beacons called Prometheus , described in detail by Group-IB specialists last year, are involved in the distribution and deployment of DarkCrystal.





