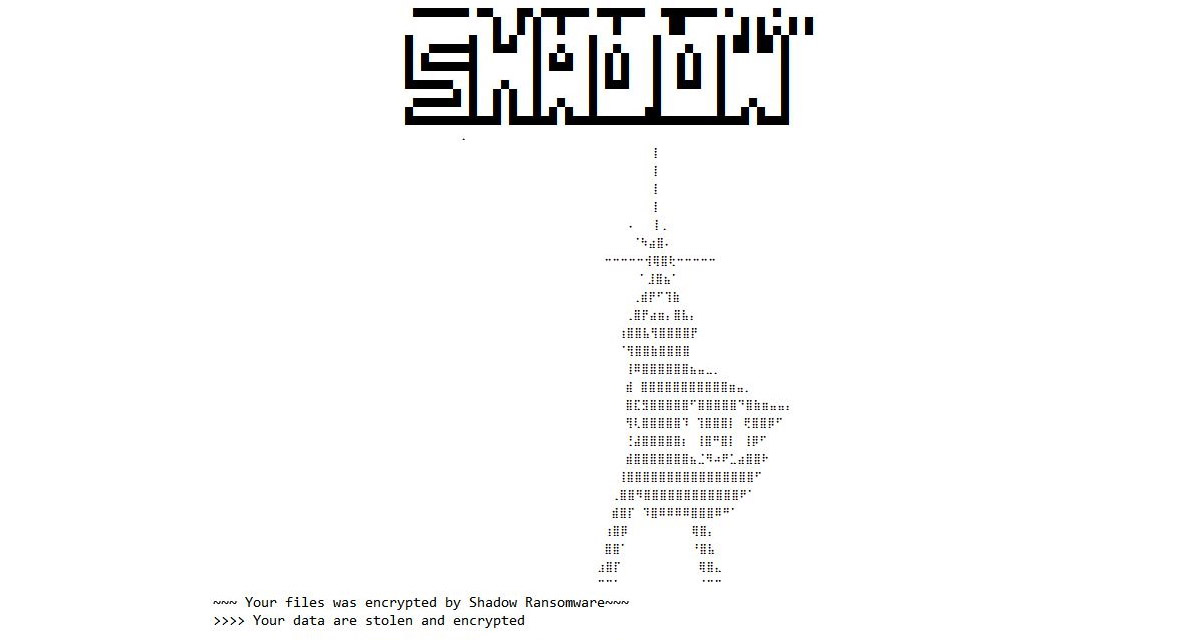
Group-IB experts have warned that the Shadow extortion group has been active since mid-March 2023. To decrypt the data, the attackers demand an amount of 1-2 million US dollars from the victims.
Experts state that the attackers penetrate the victim’s infrastructure through vulnerable public services, including RDP servers, and encrypt company data using the LockBit3 ransomware, compiled from source code that has been made publicly available. For the Linux operating system, an encryptor based on the source codes of the Babuk ransomware is used.
During the investigation, Group-IB specialists discovered that the attackers had mistakenly typed PowerShell commands on the Ukrainian keyboard layout. In addition, tools similar to those used in attacks by an unknown group on Russian banks in 2018 were identified.
To communicate with each victim, the attackers place a chat panel on the Tor network, which a representative of the attacked company can access using the private key from the ransom note. The same system of interaction with victims is used in well-known RaaS partner programs (Ransomware-as-a-Service, “Extortion as a Service”).
If the victim company refuses to pay the ransom, Shadow representatives threaten to publish the stolen data on the dark web. At the same time, the group’s representatives assure that they are not politically motivated hackers, claiming that they are only interested in money.