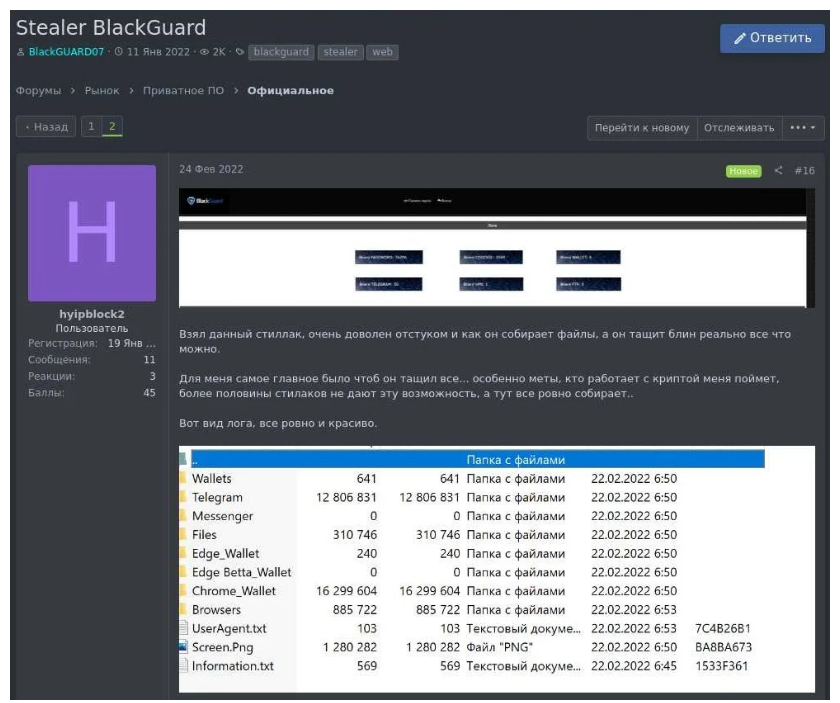
The attention of information security specialists was attracted by a new malicious software for stealing information, BlackGuard. The malware is sold on numerous marketplaces and dark web forums for $700 for a lifetime license or $200 per month.
Analysts at Zscaler have already studied the malware that became popular after the unexpected shutdown of competing malware Raccoon Stealer. In turn, Bleeping Computer reports that BlackGuard was first seen on Russian-language hack forums in January 2022, but then it was distributed privately and was at the testing stage.
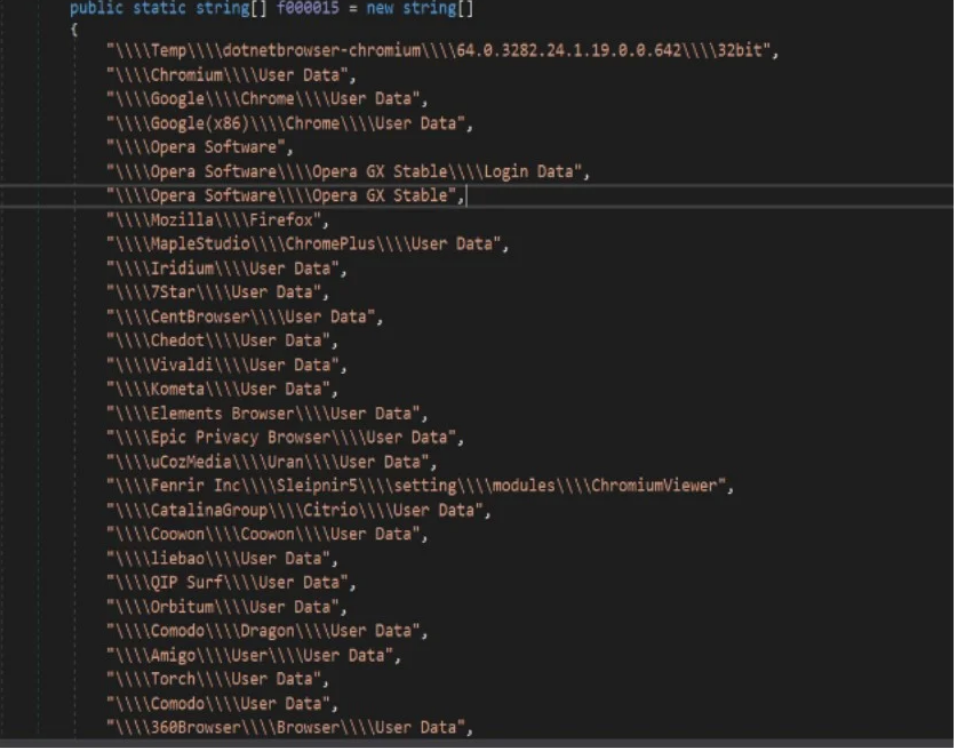
Like other modern infostealers, BlackGuard steals data from almost any application that processes sensitive user data, with a focus on cryptocurrencies. In an infected system, BlackGuard looks for the following applications, trying to steal user data from them:
- Browsers : passwords, cookies, autofill and history from Chrome, Opera, Firefox, MapleStudio, Iridium, 7Star, CentBrowser, Chedot, Vivaldi, Kometa, Elements Browser, Epic Privacy Browser, uCozMedia, Coowon, liebao, QIP Surf, Orbitum, Comodo , Amigo, Torch, Comodo, 360Browser, Maxthon3, K-Melon, Sputnik, Nichrome, CocCoc, Uran, Chromodo, Edge, BraveSoftware.
- Browser Wallets : Binance, coin98, Phantom, Mobox, XinPay, Math10, Metamask, BitApp, Guildwallet, iconx, Sollet, Slope Wallet, Starcoin, Swash, Finnie, KEPLR, Crocobit, OXYGEN, Nifty, Liquality, Auvitas wallet, Math wallet, MTV wallet, Rabet wallet, Ronin wallet, Yoroi wallet, ZilPay wallet, Exodus, Terra Station, Jaxx.
- Cryptocurrency wallets : AtomicWallet, BitcoinCore, DashCore, Electrum, Ethereum, Exodus, LitecoinCore, Monero, Jaxx, Zcash, Solar, Zap, AtomicDEX, Binance, Frame, TokenPocket, Wassabi.
- Email : Outlook.
- Messengers : Telegram, Signal, Tox, Element, Pidgin, Discord.
- Other : NordVPN, OpenVPN, ProtonVpn, Totalcommander, Filezilla, WinSCP, Steam.
The information collected from the victim is packaged in a ZIP file and sent to the attackers’ C&C server via a POST request, along with a system profile report that assigns a unique identifier to the victim’s equipment.
In terms of evading BlackGuard security solutions are still under development, but some mechanisms to avoid detection and analysis are already in place. So, the malware is packaged using a crypter, and the code is obfuscated using base64. Also, any antiviruses in the system are successfully detected by a malicious program that tries to kill their processes and stop their work.
In addition, BlackGuard checks the victim’s IP address, and if the victim works from the territory of Russia or the CIS countries, then the malware stops and exits.
Daria Romana Pop, Threat Analyst at KELA, shared her thoughts on BlackGuard with Bleeping Computer:
“The BlackGuard stealer was launched in early 2021, and cybercriminals are constantly testing the capabilities of such malicious tools and are not shy about demanding [developers] quality upgrades and other improvements. KELA has come across several threads where users have complained about BlackGuard not being able to properly avoid detection. As in any other business, the developers promised them to release an updated version as soon as possible.