According to Fortinet experts, the Dark Mirai (aka Manga or Dark.IoT) botnet operators are actively abusing a recently discovered vulnerability in TP-Link routers.
The attacks began about two weeks ago and exploit the vulnerability the CVE-2021-41653 , discovered in November of this year, the Hungarian researcher MATEK Camillo, who also unveiled a PoC-exploit.
According to Fortinet, Dark Mirai carriers use default passwords to access devices and then attack a bug found by Camillo to gain full control over unpatched TP-Link TL-WR840N routers. It should be noted that the TP-Link developers have already fixed this error with the TL-WR840N (EU) _V5_211109 firmware release on November 12, 2021, but many users still have not installed the update.
Essentially, the Dark Mirai operators use CVE-2021-41653 to force devices to download and execute the malicious tshit.sh script, which in turn downloads the main payload binaries with two requests. Since hackers still need to authenticate for the exploit to work, as mentioned above, default passwords are used.
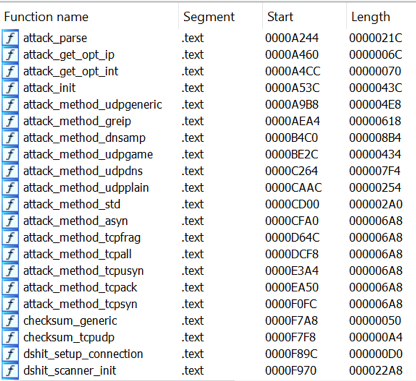
After hijacking the device, the malware blocks connections to commonly used ports to prevent other botnets from trying to hijack the router. Dark Mirai then awaits commands from its command and control server and can launch some form of DDoS attack.
Fortinet claims that operator Dark Mirai is one of the most active botnet developers to date. Since February of this year, when the botnet was first discovered , it has been constantly adopting newly discovered vulnerabilities as soon as details of these bugs appear on the network. For example, earlier in 2021, Dark Mirai already attacked routers using Arcadyan-based firmware , as well as the Realtek SDK. Moreover, these vulnerabilities were exploited only a few days after their discovery.
Other botnet attacks targeted Cisco, Tenda, DLink, and MicroFocus routers and SonicWall, Netis and Yealink devices, according to Juniper Labs and Palo Alto Networks .
Like all botnets based on Mirai, Dark Mirai is capable of carrying out DDoS attacks, as well as using infected systems as a proxy to relay malicious traffic.





