Cisco has just warned that a high-severity flaw in its network security software is being currently leveraged and exploited by threat actors.
The flaw, according to the company own PSIRT, could allow a remote and unauthenticated attacker to access sensitive data.
The San Francisco based company has already released patches for the vulnerability (CVE-2020-3452) in question.
The vulnerability has been ranked 7.5 out of a possible 10 on the CVSS scale.
This hasn’t come soon enough apparently, as Threat actors are actively targeting vulnerable versions of the software, where the patches have not yet been applied or even noted.
“The Cisco Product Security Incident Response Team (PSIRT) is aware of the existence of public exploit code and active exploitation of the vulnerability that is described in this advisory,” said Cisco in a note.
The flaw specifically exists in the web services interface of Firepower Threat Defense (FTD) software.
This is part of Cisco’s suite of network security and traffic management products.
Not only that, the CWE applies to its Adaptive Security Appliance (ASA) software too (the operating system for its family of ASA corporate network security devices).
Huston we have a problem
The potential threat surface is enormous.
According to a research done by Rapid7, 85,000 internet-accessible ASA/FTD devices are currently under threat by this vulnerability.
Even worse, nearly 400 of those are spread across 17 percent of the Fortune 500 companies.
The flaw stems from a lack of proper input validation of URLs in HTTP requests processed by affected devices.
Specifically, the flaw allows attackers to conduct directory traversal attacks, which is an HTTP attack enabling bad actors to access restricted directories and execute commands outside of the web server’s root directory.
POC and more
Right after the patches were released by Cisco, a proof-of-concept (POC) exploit code was made public Wednesday for the flaw by security researcher Ahmed Aboul-Ela.
According to this a potential attacker can view more sensitive files within the web services file system: The web services files may have information such as WebVPN configuration, bookmarks, web cookies, partial web content and HTTP URLs.
Cisco, from what we have been told by the company itself, confirms that the vulnerability affects products if they are running a vulnerable release of Cisco ASA Software or Cisco FTD Software, with a vulnerable AnyConnect or WebVPN configuration.
As you can read: “The web services file system is enabled when the affected device is configured with either WebVPN or AnyConnect features,” according to its advisory. However, “this vulnerability cannot be used to obtain access to ASA or FTD system files or underlying operating system (OS) files.”
This has been confirmed by Rapid7 that also underlined how: “Cisco has provided fixes for all supported versions of ASA and FTD components”.
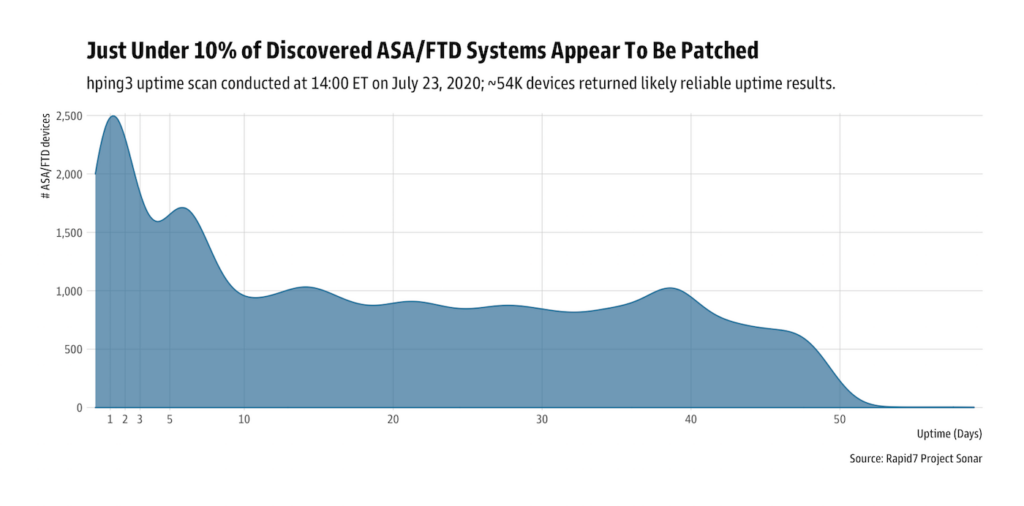
Even tho the patch has been live for quite some time, Researchers with Rapid7 warn that only about 10 percent of Cisco ASA/FTD devices detected as internet-facing have been rebooted.
The most likely indicator that they’ve been patched.
Only 27 of the 400 detected in Fortune 500 companies appear to have been done so to their services.
Researchers and Cisco alike, encourage patching of vulnerable ASA/FTD “to prevent attackers from obtaining sensitive information from these devices which may be used in targeted attacks.”
“Cisco ASA Software releases 9.5 and earlier, as well as Release 9.7, along with Cisco FTD Release 6.2.2 have reached the end of software maintenance and organizations will have to upgrade to a later, supported version to fix this vulnerability.” With threat actors on the rise, this is a clear message that needs to be heeded!





