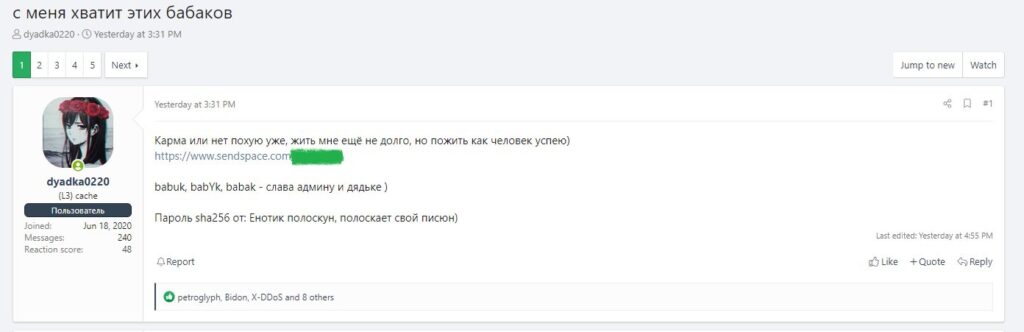
A group of vx-Underground researchers noticed that the full source code of the Babuk ransomware has been published on the Russian-language hack forum. A member of the hack group who published the source claims that he was diagnosed with stage 4 lung cancer, and he wants to have time to “live like a person.”
Let me remind you that Babuk (aka Babuk Locker and Babyk) appeared in early 2021. Malvar attacked companies, encrypted their data, and its operators also stole victims’ files and demanded a double ransom from the victims.
After the attack on the District of Columbia Central Police Department, Babuk operators received too much attention, and in April 2021, the hack group announced that it would cease operations. However, several members of the same group soon separated from the main team, renamed the malware to Babuk V2, and continue to encrypt victims’ files to this day.
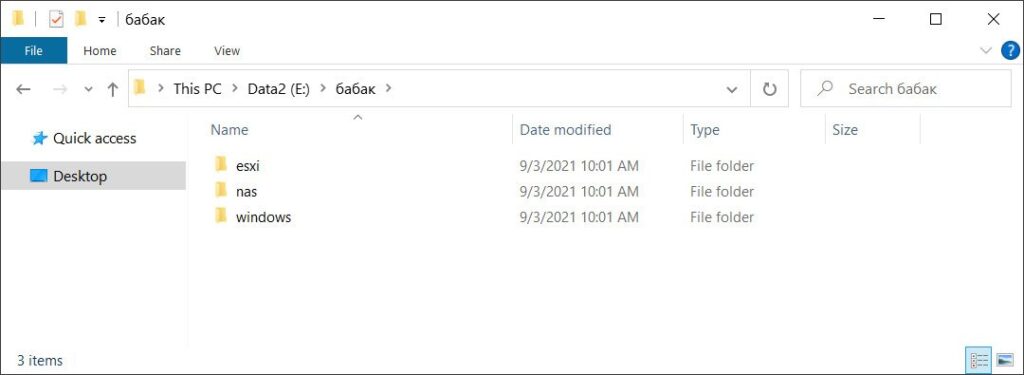
Edition Bleeping Computer reports that the file is now shared one of the members of the group, contain different Visual Studio projects to encrypt VMware ESXi, NAS, and the Windows, as shown in the screenshot below.
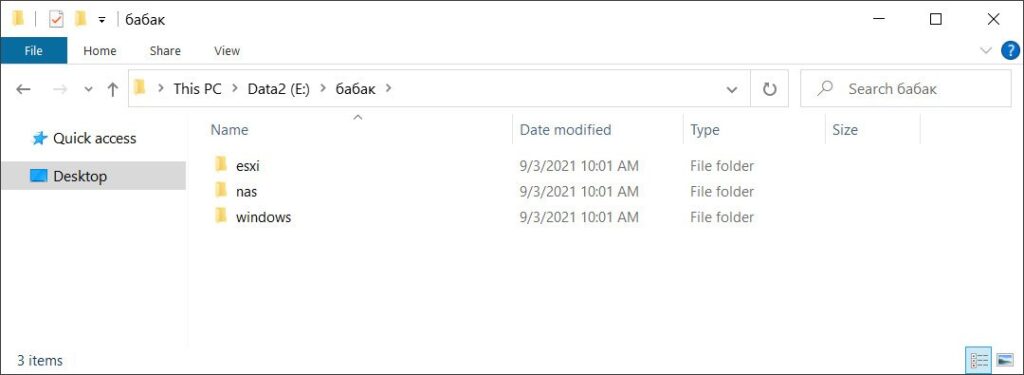
The Windows folder contains the complete malware source code, decoder code, and a private and public key generator.
Emsisoft CTO and renowned information security expert Fabian Vosar, as well as researchers from McAfee Enterprise, have already confirmed to reporters that the leak is genuine. Vosar believes that this “leak” can help decipher the data of past victims of the ransomware, but so far the researchers are only verifying this information.





