Windows, Linux, and even macOS operating systems, seems like nobody is safe from Lazarus Group new multi-platform malware framework.
Designed to infiltrate corporate entities around the world, steal customer databases, and distribute ransomware, the MATA malware framework – straight from the North Korean backed group – comes with a wide range of features designed to carry out a variety of malicious activities on infected machines.
The 18′ start
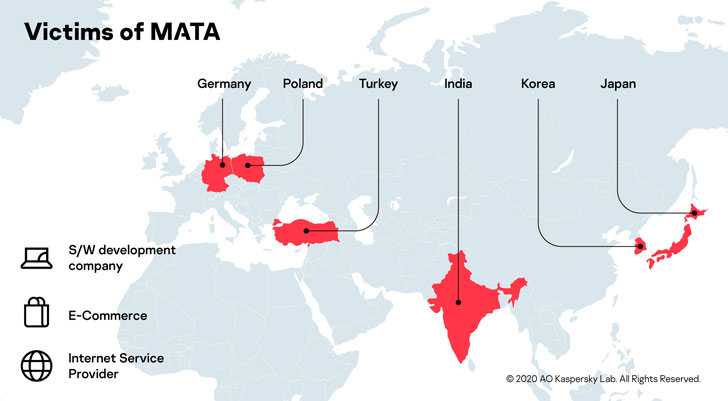
According to Kaspersky the campaign is said to have begun as early as April of 2018, with victims ranging from software development companies to ISPs and e-commerce sites.
The report from Kaspersky offers a complete look at the whole framework while continuing the work already started by Netlab 360, Jamf, and Malwarebytes.
The latest and greatest
In its latest version, the Windows version of the MATA Framework, leverages a loader to – you wouldn’t guess – load an encrypted next-stage payload: an orchestrator module (“lsass.exe”) capable of downloading at least 15 additional plugins at the same time and executing them in memory.
The plugins themselves are feature-rich, boasting features that allow the malware to manipulate files and system processes, inject DLLs, and create an HTTP proxy server.
MATA’s plugins also allow hackers to target Linux-based diskless network devices such as routers, firewalls or IoT devices, and macOS systems.
They manage to do all of this by disguising themselves as an app called TinkaOTP, which claims to be a 2FA system and its closely related – and based on – an open-source application named MinaOTP.
Once the plugins were deployed, Lazarus hackers then get to work to infiltrate the network and compromise ore steal as much data as possible.
Kaspersky hasn’t said if their attempt (or attempts) were successful but also confirmed that MATA was used to distribute VHD ransomware to one other unnamed victim.
MATA has been linked to the Lazarus Group based on the unique file name format found in the orchestrator (“c_2910.cls” and “k_3872.cls”), which has been spotted previously in several variants of the Manuscrypt malware.
Lazarus, Kim’s favorite group, (or Hidden Cobra and APT38) has been named as the culprit to many major cyber offensives, including the Sony Pictures hack in 2014, the SWIFT banking hack in 2016, and the WannaCry ransomware infection in 2017.
Most recently, the APT added web skimming to their repertoire, targeting the U.S. and European e-commerce websites to plant JavaScript-based payment skimmers.
Uncle Sam, perhaps displeased with the hacking crew’s passion for carrying out financially motivated attacks led to sanction the group and its two off-shoots, Bluenoroff and Andariel, at the of 2019.





