Sansec experts noticed that the dropper of an unnamed hack group infecting online stores with MageCart malware (web skimmers) contains a list of compromised sites.
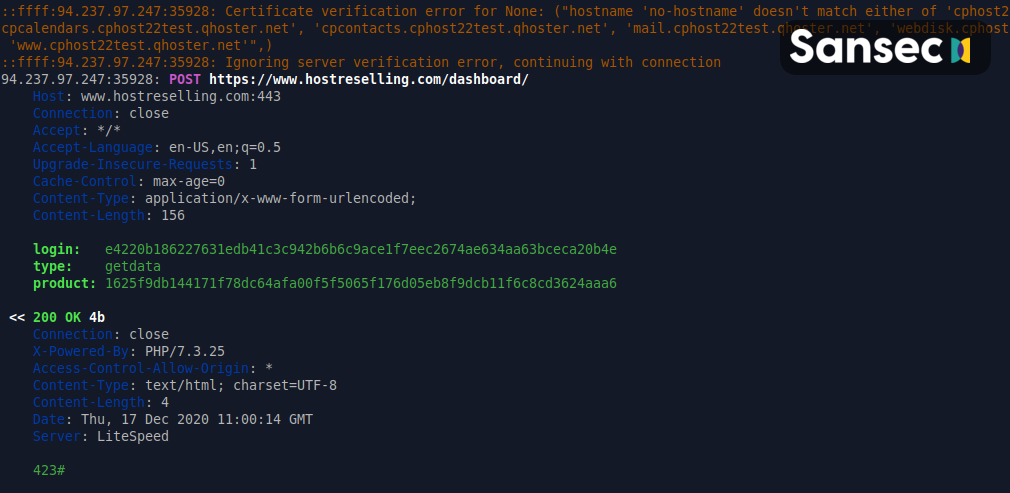
The dropper was used by criminals to deploy RAT malware on compromised sites. With the help of this malware, the criminals achieved a stable presence in the victim’s system and used it to restore access to the servers of hacked online stores, on whose pages web skimmers were embedded.
The researchers say that the malware was delivered using a PHP dropper as a 64-bit ELF executable file. To avoid detection and complicate analysis, the RAT masqueraded as a DNS or SSH server daemon and did not appear in the server process list. Also, for most of the day, the malware was in sleep mode and “woke up” only once a day, at 7 am in order to connect to the C&C server and request commands.
The RAT samples obtained by Sansec from several compromised servers were compiled for attacks on Ubuntu and Red Hat Linux.
However, despite the use of advanced RAT malware, the hackers made a gross mistake by including the list of hacked online stores in their dropper code. For example, Sansec experts studied the dropper and, in addition to the expected malicious code, found that it contains addresses of 41 hacked online stores. The researchers believe that this happened due to the fact that the dropper was written by an attacker who has little experience with PHP.

Researchers have already contacted all of the affected stores from the found list and warned their owners about the compromise.





