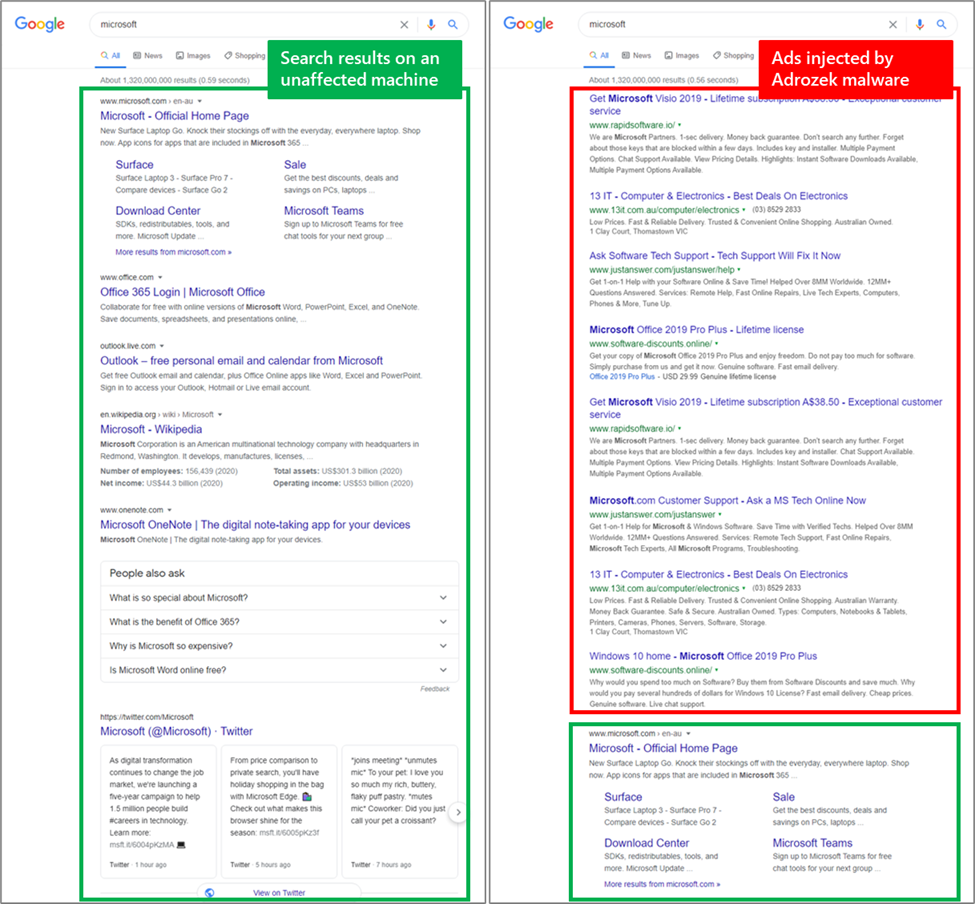
Microsoft has warned of the emergence of a new malware called Adrozek , which infects users’ devices and alters their browser settings to serve ads in search results.
According to the company, the malware has been active since at least May of this year and peaked in August, when it monitored more than 30,000 infected browsers every day. However, analysts believe that the real number of infected users is much higher, because in the period from May to September 2020, experts recorded “hundreds of thousands” of Adrozek detections around the world.
Europe appears to be the hardest hit by the new threat, followed by South and Southeast Asia.
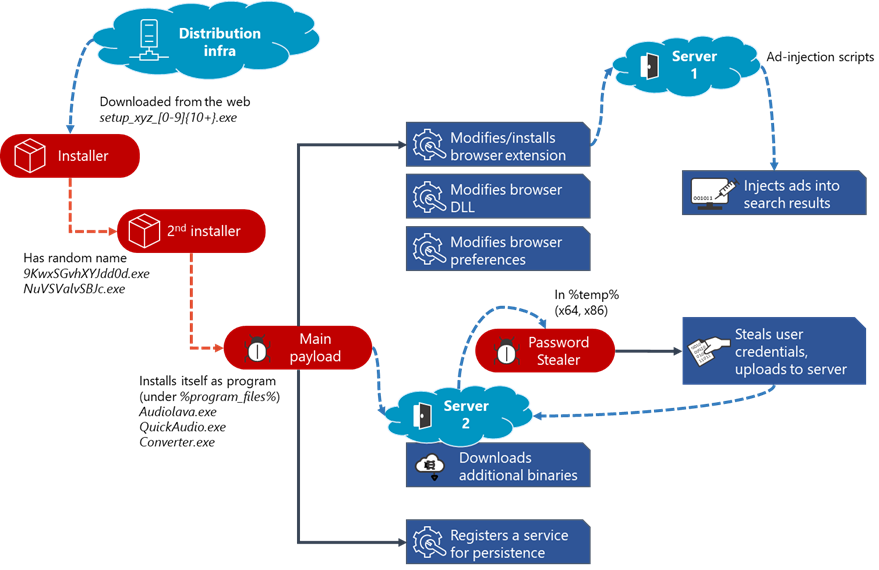
Currently, malware is spread using classic drive-by attacks. That is, users are redirected from legitimate sites to the domains of the attackers, where they are tricked into installing malware, which then ensures itself a permanent presence in the system by registering in the registry.
Once in the system, Adrozek will search for locally installed browsers, including Microsoft Edge, Google Chrome, Mozilla Firefox, and Yandex Browser. If a target has been detected, the malware tries to forcibly install its extension by modifying the AppData folder. To ensure that browser protection does not work and does not detect unauthorized modifications, Adrozek also modifies some browser DLLs, settings and disables security mechanisms. So, the malware makes the following changes:
- disables browser updates;
- disables file integrity checks;
- disables safe browsing features;
- registers and activates the extension added in the previous step;
- allows a malicious extension to run in incognito mode;
- allows you to launch the extension without obtaining the appropriate rights;
- hides the extension from the toolbar;
- changes the browser’s default home page;
- changes the default search engine.
All of this is done so that Adrozek can advertise on search results pages. Due to this advertising, malware operators receive income by directing traffic to advertising sites or referral programs.
Worse, in the case of Firefox, the malware also extracts credentials from the browser and sends them to the attackers’ server.
Microsoft writes that Adrozek’s operations are extremely complex, especially when it comes to distribution infrastructure. Since May 2020, the company has tracked 159 domains that hosted Adrozek installers. Each domain hosted an average of 17,300 dynamically generated URLs, and each URL hosted over 15,300 dynamically generated Adrozek installers.
“While many of the domains contained tens of thousands of URLs, some had over 100,000 unique URLs, and on one we found nearly 250,000 URLs. This huge infrastructure reflects the determination of the attackers to keep this campaign running. Some of these domains have been active for only one day, while others have been active for much longer (up to 120 days), ”the experts write, adding that in the coming months, the scale of Adrozek’s operations is likely to increase even more.





